In the high-stakes environment of web administration, the arrival of an 'urgent' security advisory from an official-looking source often triggers an immediate reactive response. Attackers are increasingly weaponizing this trust through sophisticated phishing campaigns that masquerade as official WordPress security updates. By leveraging fabricated vulnerabilities and professional-grade social engineering, cybercriminals are successfully tricking administrators into installing the very 'patches' that compromise their servers. This is not just a simple scam; it is a calculated intrusion strategy designed to establish persistent, high-level access to the heart of your digital infrastructure.
The Phishing Epidemic: Weaponizing Security Trust
Phishing remains the primary entry point for over 90% of successful data breaches, and its effectiveness in the WordPress ecosystem is growing. The current campaign targets the specific fear of a Zero-Day exploit. Unlike generic spam, these emails are crafted with a level of technical jargon that makes them indistinguishable from official communication to the untrained eye. They often reference a critical security flaw that requires immediate attention to prevent site defacement or data theft, creating a 'false sense of urgency' that overrides standard verification protocols.
When an administrator is told their site is currently vulnerable, their first instinct is to secure it. This cognitive bias is exactly what the attackers exploit. Instead of redirecting to a fake login page, this campaign directs users to a meticulously cloned 'official' download portal, where they are prompted to install a 'Security Patch' in the form of a custom WordPress plugin. This shift from credential theft to malicious software installation marks a significant escalation in the complexity of modern phishing tactics.
Dissecting the CVE-2023-45124 Hoax
The core of this deception is the citation of a non-existent vulnerability: CVE-2023-45124. To an experienced security analyst, the ID is an immediate red flag, but for a busy site owner, a CVE ID adds a layer of unearned authority to the email. The attackers even go as far as creating fake security blogs and 'Proof of Concept' pages that appear in search results for the fabricated ID, ensuring that even if the administrator does a quick search, they cross-reference the lie with more lies.
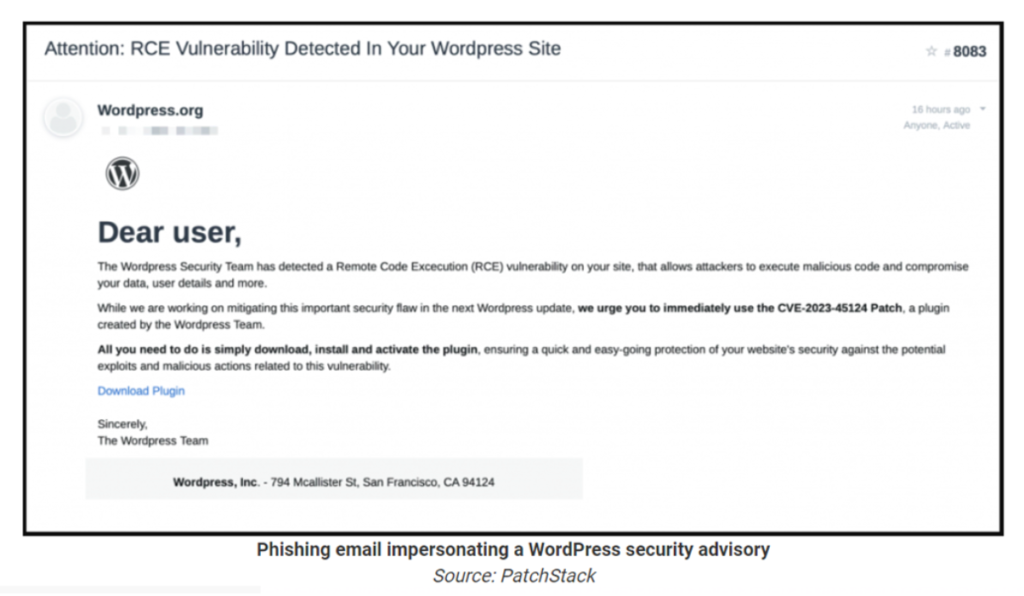
This level of preparation demonstrates a clear understanding of application security workflows. The attackers know that a professional admin will look for a CVE reference, so they provide one. This 'hoax-driven' infiltration strategy bypasses many traditional email filters that primarily scan for malicious attachments or known phishing URLs, as the initial link often points to a reputable cloud storage service or a newly registered, SSL-certified domain that hasn't yet been flagged.
Technical Payload Analysis: Beyond the 'wpsecuritypatch' Admin User
Once the 'wp-securitypatch' plugin is activated, the compromise is near-instantaneous. The plugin's primary function is to bypass the standard authentication layer and create a hidden administrative user account. This account typically uses a name that blends into the system logs, such as 'wp-support' or 'system-admin,' and is often hard-coded to ignore standard notification triggers that would alert the site owner to a new user creation.
The Hidden Mechanisms of Persistence
Creation of a user is only the beginning. The malicious plugin establishes a persistent backdoor through the use of obfuscated PHP eval() functions or by modifying the .htaccess file to allow remote shell execution. This grants the attacker a 'command and control' (C2) channel that bypasses the WordPress dashboard entirely. Even if the plugin is deactivated, the backdoor often remains embedded in the core file structure, allowing the attacker to re-enter the system at will. This level of persistence is a standard feature in modern malware analysis reports, where 'ghost' processes continue to infect the site long after the initial entry vector is removed.

This persistent access is used for more than just defacement. It is a gateway for 'lateral movement' within a server environment. If your site is hosted on a shared platform, a single backdoor can be used to probe neighboring accounts, turning your site into a launching pad for a wider offensive. This significantly increases your liability and can lead to permanent damage to your reputation guard status with your hosting provider and your customers.
Verification Protocols: How to Authenticate Security Advisories
To defend against these weaponized advisories, organizations must establish a strict protocol for software updates. Official WordPress security updates are almost never communicated through unsolicited email. They are either pushed through the WordPress dashboard as an automated update or announced on the official WordPress.org news blog. If an advisory contains a direct download link to a ZIP file instead of directing you to the official repository, it should be treated as malicious until proven otherwise.
Furthermore, verify every CVE reference through the official MITRE or NVD databases. If the ID does not exist or is marked as 'reserved' without any description, the advisory is a hoax. In a professional managed security environment, no patch is applied until it has been vetted in a staging environment and its source has been cryptographically verified. If you aren't 100% sure about the source of a patch, do not install it.
Neutralize the Threat to Your CMS
Cybercriminals are counting on your sense of urgency to bypass your common sense. If you have already interacted with a suspicious update or noticed unusual administrative activity on your WordPress site, you must act immediately to prevent a full-scale data breach. Our security team specializes in the deep-level malware analysis and forensic restoration needed to identify and remove persistent backdoors. Reach out to our WordPress security experts today for a comprehensive compromise assessment and ensure that your digital assets remain under your control, and not a hacker's.
